Abstract
The optimal pixel expansion is an important parameter of deterministic visual cryptography scheme (DVCS). There are many researches have been done under different access structures and stacking operations. However, any necessary or sufficient condition has not been found about the optimal pixel expansion. In this paper, we give a necessary condition of the optimal pixel expansion of DVCS for the first time, which is suitable for any access structure and any stacking operation. Furthermore, a pixel expansion optimization algorithm has been designed to improve the existing schemes. It is found that the pixel expansion can be reduced for most DVCS based on XOR operation. Finally, we give some experimental results and comparisons to show the effectiveness of the proposed scheme.



Similar content being viewed by others
References
Ateniese G, Blundo C, De Santis A, Stinson DR (1996) Visual cryptography for general access structures. Inf Comput 129(2):86–106
Biham E, Itzkovitz A (1997) Visual cryptography with polarization. In The Dagstuhl Seminar on Cryptography
Blakley GR (1979) Safeguarding cryptographic keys. In Proceedings of the National Computer Conference, NJ, USA, 48:242–268
Cimato S, De Prisco R, De Santis A (2006) Probabilistic visual cryptography schemes. Comput J 49(1):97–107
Cimato S, De Prisco R, De Santis A (2007) Colored visual cryptography without color darkening. Theor Comput Sci 374(1–3):261–276
Cimato S, de Santis A, Ferrara AL, Masucci B (2005) Ideal contrast visual cryptography schemes with reversing. Inf Process Lett 93:199–206
De Prisco R, De Santis A (2011) Using colors to improve visual cryptography for black and white images. In ICITS 2011, Springer, LNCS 6673:182–201
Droste S (1996) New results on visual cryptography. In Proc. Advances in Cryptography-CRYPTO’96. pp 401–415
Horng G, Chen T, Tsai D (2006) Cheating in visual cryptography. Des Codes Crypt 38:219–236
Ito R, Kuwakado H, Tanaka H (1999) Image size invariant visual cryptography. IEICE Trans Fundam Electron Commun Comput Sci E82A(10):2172–2177
Katoh T, Imai H (1998) An extended construction method for visual secret sharing schemes. Electron Commun Jpn (Part III: Fundam Electron Sci) 81:55–63
Lee K, Chiu P (2011) A high contrast and capacity efficient visual cryptography scheme for the encryption of multiple secret images. Opt Commun 284:2730–2741
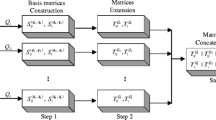
Liu F, Wu C, Lin X (2010) Step construction of visual cryptography schemes. IEEE Trans Inf Forensic Secur 5:27–38
Liu F, Wu CK, Lin X (2011) Cheating immune visual cryptography scheme. IET Inf Secur 5(1):51–59
Naor M, Shamir A (1995) Visual cryptography. Advances in cryptology-eurocrypt’94. Berlin, LNCS 950:1–12
Shamir A (1979) How to share a secret. Commun ACM 22(11):612–613
Shyu SJ, Chen MC (2011) Optimum pixel expansions for threshold visual secret sharing schemes. IEEE Trans Inf Forensic Secur 6(3):960–969
Tuyls P, Hollmann HDL, van Lint JH, Tolhuizen L (2005) Xor-based visual cryptography schemes. Des Codes Crypt 37:169–186
Tuyls P, Kevenaar T, Schrijen GJ, Staring T, Dijk MV (2004) Security displays enabling secure communications. In First Int. Conf. Pervasive Computing, Boppard, Germany, vol 2802. Berlin Springer LNCS, pp 271–284
Wang DS, Yi F, Li XB (2009) On general construction for extended visual cryptography schemes. Pattern Recognit 42(11):3071–3082
Weir J, Yan W (2012) Visual cryptography and its applications. Ventus Publishing ApS, Denmark
Yang CN (2004) New visual secret sharing schemes using probabilistic method. Pattern Recognit Lett 25:481–494
Yang CN, Chen TS (2005) Size-adjustable visual secret sharing schemes. IEICE Trans Fundam E88-A(9):2471–2474
Yang CN, Chung T (2010) A general multi-secret visual cryptography scheme. Opt Commun 283:4949–4962
Yang CN, Wang CC, Chen TS (2006) Real perfect contrast visual secret sharing schemes with reversing. ACNS 2006, LNCS, pp 433–447
Yang CN, Wang CC, Chen TS (2008) Visual cryptography schemes with reversing. Comput J 51:710–722
Acknowledgments
The authors would like to thank the anonymous reviewers for their valuable comments. This work was supported by National Natural Science Foundation of China under Grant No. 61070086.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Fu, Z., Yu, B. Optimal pixel expansion of deterministic visual cryptography scheme. Multimed Tools Appl 73, 1177–1193 (2014). https://doi.org/10.1007/s11042-013-1625-3
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-013-1625-3