Abstract
Real-time video streams require an efficient encryption method to ensure their confidentiality. One of the major challenges in designing a video encryption algorithm is to encrypt the vast amount of video data in real-time to satisfy the stringent time requirements. Video encryption algorithms can be classified according to their association with video compression into joint compression and encryption algorithms and compression-independent encryption algorithms. The latter have a clear advantage over the former regarding the incorporation into existing multimedia systems due to their independence of the video compression. In this paper we present the compression-independent video encryption algorithm Puzzle, which was inspired by the children game jigsaw puzzle. It comprises two simple encryption operations with low computational complexity: puzzling and obscuring. The scheme thereby dramatically reduces the encryption overhead compared to conventional encryption algorithms, such as AES, especially for high resolution video. Further outstanding features of Puzzle are a good trade-off between security demands and encryption efficiency, no impairment on video compression efficiency, and an easy integration into existing multimedia systems. This makes Puzzle particularly well-suited for these security-sensitive multimedia applications, such as videoconferencing, where maximal security and minimal encryption overhead are desired simultaneously.











Similar content being viewed by others
References
Agi I and Gong L (1996) An Empirical Study of MPEG Video Transmission. In: Proc. of the Internet Society Symposium on Network and Distributed System Security, San Diego, CA, USA, pp.137–144
Bellare M, Desai A, Jokipii E, Rogaway P (1997) A Concrete Security Tretment of Symmetric Encryption: Analysis of the DES Modes of Operation. In: IEEE Proceedings of the 38th Symposium on Foundations of Computer Science
Bernstein DJ: Salsa20 Design. http://cr.yp.to/snuffle/design.pdf
BRAVIS Video Conference System: http://www.bravis-gmbh.de/en/unternehmen.html
Coskun B, Sankur B, Memon N (2006) Spatio-temporal transform based video hashing. IEEE Trans Multimed 8 6:1190–1208
Durstenfeld R (1964) Algorithm 235: random permutation. Commun ACM 7 7:420
Dworkin M (2001) Recommendation for Block Cipher Modes of Operation, Methods, and Techniques. NIST Special Publication 800-38A
Fuhrt and Kirovski D: Eds. Multimedia Security Handbook, CRC Press, 2004
Haskell BG, Puri A, and Netravali AN (1996) Digital Video: an Introduction to MPEG-2. Kluwer Academic Publishers
Jakimoski G, Subbalakshmi KP (2008) Cryptanalysis of some multimedia encryption schemes. IEEE Trans Multimed 10 3:330–338
Johnathan MR, and David GM (2001) The Impact of Confidentiality on Quality of Service in Heterogeneous Voice over IP Networks. LNCS 2216, Springer
Katz J and Lindell Y (2008) Introduction to Modern Cryptography. Chapman&Hall/CRC
Knuth DE (1981) The Art of Computer Programming, 2nd Edition. Vol. 2: Semi-numerical Algorithms. Addison- Wesley
Krawczyk H, Bellare M, and Canetti R (1997) HMAC: Keyed-Hashing for Message Authentication, RFC 2104
Li S, Chen G, Cheung A, Bhargava B, Lo KT (2007) On the design of perceptual MPEG-video encryption algorithms. IEEE Trans Circ Syst Video Tech 17 2:214–223
Li Y, Chen Z, Tan S-M, and Campbell RH (1996) Security Enhanced MPEG Player. In: Proc. of the 1st IEEE International Workshop on Multimedia Software Development (MMSD`96), Washington DC, USA, pp. 169–176
Liu X and Eskicioglu AM (2003) Selective Encryption of Multimedia Content in Distribution Networks: challenges and New Directions. IASTED International Conference on Communications, Internet and Information Technology (CIIT), Scottsdale, AZ, USA
Liu F, Koenig H (2005) A Novel Encryption Algorithm for High Resolution Video. In: Proc. of ACM NOSSDAV’05, Stevenson, WA, USA. ACM Press, New York, pp 69–74
Liu F and Koenig H (2005) Puzzle - A Novel Video Encryption Algorithm. IFIP CMS’05, Salzburg, Austria, Sept. 2005, LNCS 3677, Springer, pp.88–97
Liu F, Koenig H (2010) A survey of video encryption algorithms. Comput Secur 29 1:3–15
Mayer-Patel K, Smith BC, Rowe LA (2005) The berkeley software MPEG-1 video decoder. ACM Trans Multimed Comput, Commun Appl 1 1:110–125
Menezes AJ, Oorschot PC van , and Vanstone SA (1997) Handbook of Applied Cryptography. CRC Press Series on Discrete Mathematics and its Applications. CRC Press
Moses LE, and Oakford RV (1963) Tables of Random Permutations. Stanford University Press
NIST (2001) Advanced Encryption Standard, FIPS PUB 197
NIST SP 800-57 (2007) Recommendation for Key Management (Revised)
OMAP 3530 Applications Processor: http://focus.ti.com/lit/ds/symlink/omap3530.pdf
Pommer A and Uhl A (2002) Application scenarios for selective encryption of visual data. In: Proc. of the Multimedia and Security Workshop at ACM Multimedia, pp 71–74
Qiao L and Nahrstedt K (1997)Is MPEG Encryption by Using Random List Instead of Zigang Order Secure? In: Proc. of the IEEE International Symposium on Consumer Electronics, Singapore, pp.226-229
Qiao L, Nahrstedt K (1998) Comparison of MPEG encryption algorithms. Comput Graph 22 4:437–448
Rogaway P, Coppersmith D (1993) A software-optimized encryption algorithm. Proceedings of the 1st International Workshop on Fast Software Encryption. Springer, Cambridge, pp 56–63
Rueppel RA (1986) Analysis and Design of Stream Ciphers. Springer
S Goldwasser and M Bellare: Lecture Notes on Cryptography. http://cseweb.ucsd.edu/users/mihir/papers/gb.html
Schneier R (1996) Applied cryptography. Wiley, New York
Shi C, Wang SY and Bhargava B (1999): MPEG Video Encryption in Real-Time Using Secret Key Cryptography. In: Proc. of the International Conference on Parallel and Distributed Processing Techniques and Applications (PDPTA’99), Las Vegas, NV, USA, pp. 2822–2828
Socek D, Magliveras S, Ćulibrk D, Marques O, Kalva H, and Furt B (2007) Digital Video Encryption Algorithms Based on Correlation-Preserving Permutations. EURASIP Journal on Information Security, Volume 2007, Issue 1
Spanos GA and Maples TB (1995) Performance Study of a Selective Encryption Scheme for the Security of Networked Real-time Video. In: Proc. of the 4th International Conference on Computer Communication and Networks (ICCCN` 95), Las Vegas, NV, USA, pp. 2–10
Stanek M and Stanekova L (2006) Unpuzzling Puzzle (Analysis of a video encryption algorithm). In: Proc. of 2nd IEEE International Workshop on Security in Networks and Distributed Systems (SNDS-06), Vienna, Austria, pp.20–24
Tang L (1996) Methods for encrypting and decrypting MPEG video data efficiently. ACM International Conference on Multimedia, Boston, MA, USA, pp.219–229
Tektronix. ftp://ftp.tek.com/tv/test/streams/Element/index.html
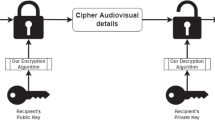
Wu CP, Kuo C-CJ (2000) Fast encryption methods for Audiovisual Data Confidentiality. SPIE International Symposia on Information Technologies, Vol. 4209, Boston, pp 284–295
Wu C-P, Kuo C-CJ (2005) Design of integrated multimedia compression and encryption systems. IEEE Trans Multimed 7(5):828–839
Zeng W, Lei S (2003) Efficient frequency domain selective scrambling of digital video. IEEE Trans Multimed 5 1:118–129
Zhou J, Liang Z, Chen Y, Au OC (2007) Security analysis of multimedia encryption schemes based on multiple Huffman table. IEEE Signal Process Lett 14 3:201–204
Acknowledgment
We would like to thank M. Stanek and L. Stanekova for their constructive comments on our previous schemes. We also thank anonymous referees for their very helpful comments to improve the quality of this paper.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Liu, F., Koenig, H. Puzzle - an efficient, compression independent video encryption algorithm. Multimed Tools Appl 73, 715–735 (2014). https://doi.org/10.1007/s11042-012-1185-y
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-012-1185-y