Abstract
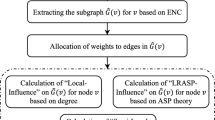
Mobile ad hoc social networks are self-configuring social networks that connect users using mobile devices, such as laptops, PDAs, and cellular phones. These social networks facilitate users to form virtual communities of similar interests or commonalities. This paper proposes semantics-based mobile social network (SMSN), a novel framework of a fully functional mobile ad hoc social network that incorporates semantics of users’ social data. SMSN provides effective and efficient solutions to social network construction, semantics-based user profile matching, multi-hop semantics-based routing, and privacy management. Moreover, SMSN is rigorously benchmarked using an elaborate simulation setup and released as a prototype system that can be run on cellular phones. Due to its generality, SMSN can be applied to a wide range of critical applications, such as disaster-recovery, homeland security, and personnel control.












Similar content being viewed by others
References
Atallah MJ, Du W (August 8–10 2001) Secure multi-party computational geometry. In Seventh International Workshop on Algorithms and Data Structures (WADS 2001), Providence, Rhode Island, USA.
Baader F, Calvanese D, McGuinness DL, Nardi D, Patel-Schneider PF (2003) The description logic handbook: theory, implementation, applications. Cambridge University Press, Cambridge
Bettstetter C, Wagner C (2002) The spatial node distribution of the random waypoint mobility model. In Proc. WMAN.
Bluepulse website: http://www.bluepulse.com/.
Clausen T, Jacquet P (October 2003) Optimized Link State Routing Protocol (OLSR). RFC 3626, IETF Network Working Group.
Chiang CC, Wu HK, Liu W, Gerla M (April 1997) Routing in clustered multihop, mobile wireless networks with fading channel. Proceedings of IEEE Singapore International Conference on Networks (SICON), Singapore.
Damgard I, Jurik M (2001) A generalisation, a simplification and some applications of Paillier’s probabilistic public-key system. In 4th International Workshop on Practice and Theory in Public Key Cryptosystems (PKC ’01), LNCS 1992, pp 119–136.
Dodge ball website: http://www.dodgeball.com/.
Du W, Atallah MJ (December 10–14 2001) Privacy-preserving statistical analysis. In Proceeding of the 17th Annual Computer Security Applications Conference, New Orleans, Louisiana, USA.
Freedman M, Nissim K, Pinkas B (May 2004) Efficient private matching and set intersection. In Advances in Cryptology – Eurocrypt ’04, volume 3027 of LNCS, pp 1–19. Springer-Verlag.
Goldreich O, Micali S, Wigderson A (1987) How to play any mental game - a completeness theorem for protocols with honest majority. In 19th ACM Symposium on the Theory of Computing, pp 218–229.
Gruber TR (1995) Principles for the design of ontologies used for knowledge sharing. Int J Hum-Comput Stud 907–928.
Gruver WA, Boudreaux JC (1993) Intelligent manufacturing: programming environments for CIM. Springer-Verlag, London
FOAF webiste: http://www.foaf-project.org/.
Haas Z, Pearlman M, Samar P (2002) Zone Routing Protocol (ZRP). IETF Internet Draft.
Haas Z, Halpern J, Li L (2002) Gossip based ad hoc routing. In Proc. Of INFOCOM.
Jaiku website: http://www.jaiku.com/.
Jambo Networks: http://www.jambo.net.
Jiang J, Conrath D (1997) Semantic similarity based on corpus statistics and lexical taxonomy. In Proceeding of the Int’l Conf. Computational Linguistics (ROCLING X).
Jiang M, Li J, YC Tay YC (July 1999) Cluster Based Routing Protocol (CBRP) functional specification. IETF Internet Draft, draft-ietf-manet-cbrp-spec-01.txt.
Joa-Ng M, Lu I (1999) A peer-to-peer zone-based two-level link state routing for mobile ad hoc networks. IEEE J Sel Area Comm 17(8):1415–1425
Johnson D, Maltz D, Hu Y-C (July 2004) The dynamic source routing protocol for mobile ad hoc networks. Internet Draft, draft-ietfmanet-dsr-10.txt.
Kantarcıoglu M, Clifton C (2004) Privacy-preserving distributed mining of association rules on horizontally partitioned data. IEEE Trans Knowl Data Eng 16(4).
Kissner L, Song D (August 2005) Private and threshold set-intersection. In Advances in Cryptology – CRYPTO’05.
Lee J, Kim M, Lee Y (1993) Information retrieval based on conceptual distance in IS-A hierarchies. J Doc 49:188–207
Lenders V, May M, Plattner B (2005) Service discovery in mobile ad hoc networks: a field theoretic approach. In Proc. of the WoWMoM.
Li J, Vuong S (2006) Grid resource discovery based on semantic P2P communities. In Proc. of the 21st ACM SAC, pp 754-759.
Li J (2009) Building distributed index for semantic web data. In Proc. of the 23rd IEEE AINA.
Li J, Vuong S (2008) SOON: a scalable self-organized overlay network for distributed information retrieval. In Proc. of the 19th IFIP/IEEE DSOM. pp 1-13.
Murthy S, Garcia-Luna-Aceves JJ (November 1995) A routing protocol for packet radio networks. Proceedings of the First Annual ACM International Conference on Mobile Computing and Networking, Berkeley.
MobiLuck: http://www.mobiluck.com/.
Ni S, Tseng Y, Chen Y, Sheu J (1999) The broadcast storm problem in a mobile ad hoc network. Proc. of the 5th ACM/IEEE MobiCom, pp 151-162.
Nokia Sensor: http://www.nokia.com/.
Ogier R, Templin F, Lewis M (February 2004) Topology dissemenation based on reverse-path forwarding (TBRPF). http://www.ietf.org/rfc/rfc3684.txt, Internet Draft, IETF.
OWL Web Ontology Language: http://www.w3.org/TR/owl-features/.
Paillier P (1999) Public-key cryptosystems based on composite degree residuosity classes. Advances in Cryptology – EUROCRYPT 1999, LNCS 1592:223–238.
Park VD, Corson MS (April 2002) Temporally-Ordered Routing Algorithm (TORA) version 1: functional speciations. Internet draft, draft-ietfmanet-tora-spec-01.txt.
Pedersen T, Patwardhan S, Michelizzi J (2004) WordNet: similarity-measuring the relatedness of concepts. In Proc of AAAI.
Perkins CE, Watson TJ (1994) Highly Dynamic Destination Sequenced Distance Vector Routing (DSDV) for mobile computers. In Proc of ACM SIGCOMM, pp 234–244.
Perkins C, Belding-Royer E, Das S (2003) Ad hoc On-Demand Distance Vector (AODV) routing. RFC 3561.
Plazes website: http://plazes.com/.
Rada R, Mili H, Bicknell E, Blettner M (1989) Development and application of a metric on semantic nets. IEEE Trans Syst Man Cybern.
Resource Description Framework (RDF): http://www.w3.org/RDF/.
Santivanez CA, Stavrakakis I, Ramanathan R (October, 2001) Making linkstate routing scale for ad hoc networks. In: Proceedings of MobiHoc 2001, Long Beach.
Schneier B (1995) Applied cryptography, 2nd edn. Wiley.
SMSN website, http://www.cs.ndsu.nodak.edu/~juali/MobiSN.html.
von Hessling A, Kleemann T, Sinner A (2–2005) Semantic user profiles and their applications in a mobile environment. Fachberichte Informatik.
Wu Z, Palmer M (1994) Verb semantic and lexical selection. In Proc. of the 32nd Annual Meeting of the Association for computational Linguistics.
Yao AC (1986) How to generate and exchange secrets. In Proceedings of the 27th IEEE Symposium on Foundations of Computer Science, pp 162–167. IEEE.
SMSN open source Google Code website, http://code.google.com/p/mobisn/.
May M, Karlsson G, Lenders V (2007) A system architecture for delay-tolerant content distribution. In WRECOM.
Bottazzi D, Montanari R, Toninelli A (2007) Context-aware middleware for anytime, anywhere social networks. IEEE Intel Syst 22(5):23–32
Beale R (2005) Supporting social interaction with smart phones. IEEE Pervasive Computing 4(2):35–41
Korhonen VA, Pyykkönen R (2009) Creating context as you go. In Procs. of the 13th International MindTrek Conference: Everyday Life in the Ubiquitous Era, pp 37–40.
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Li, J., Wang, H. & Khan, S.U. A Semantics-based Approach to Large-Scale Mobile Social Networking. Mobile Netw Appl 17, 192–205 (2012). https://doi.org/10.1007/s11036-011-0330-6
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11036-011-0330-6