Abstract
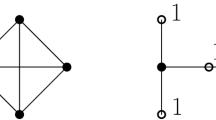
In a graph \(G=(V,E)\), a set \(D \subseteq V\) is said to be a dominating set of G if for every vertex \(u\in V{\setminus }D\), there exists a vertex \(v\in D\) such that \(uv\in E\). A secure dominating set of the graph G is a dominating set D of G such that for every \(u\in V{\setminus }D\), there exists a vertex \(v\in D\) such that \(uv\in E\) and \((D{\setminus }\{v\})\cup \{u\}\) is a dominating set of G. Given a graph G and a positive integer k, the secure domination problem is to decide whether G has a secure dominating set of cardinality at most k. The secure domination problem has been shown to be NP-complete for chordal graphs via split graphs and for bipartite graphs. In Liu et al. (in: Proceedings of 27th workshop on combinatorial mathematics and computation theory, 2010), it is asked to find a polynomial time algorithm for computing a minimum secure dominating set in a block graph. In this paper, we answer this by presenting a linear time algorithm to compute a minimum secure dominating set in block graphs. We then strengthen the known NP-completeness of the secure domination problem by showing that the secure domination problem is NP-complete for undirected path graphs and chordal bipartite graphs.


Similar content being viewed by others
References
Aho AV, Hopcroft JE, Ullman JD (1974) The design and analysis of computer algorithm. Addison-wesley, Reading
Booth KS, Johnson JH (1974) Dominating sets in chordal graphs. SIAM J Comput 9:205–212
Brandstädt A, Le VB, Spinrad JP (1999) Graph classes: a survey. SIAM, Philadelphia
Burger AP, Cockayne EJ, Gründlingh WR, Mynhardt CM, van Vuuren JH, Winterbach W (2004) Finite order domination in graphs. J Comb Math Comb Comput 49:159–175
Burger AP, Henning MA, van Vuuren JH (2008) Vertex covers and secure domination in graphs. Quaest Math 31:12–17
Burger AP, de Villiers AP, van Vuuren JH (2013) Two algorithms for secure graph domination. J Comb Math Comb Comput 85:321–339
Burger AP, de Villiers AP, van Vuuren JH (2014) A linear algorithm for secure domination in trees. Discrete Appl Math 171:15–27
Burger AP, de Villiers AP, van Vuuren JH (2015) Edge criticality in secure graph domination. Discrete Optim 18:111–122
Burger AP, de Villiers AP, van Vuuren JH (2016) On mimimum secure dominating sets of graphs. Quaest Math 39:189–202
Chen L, Lu C, Zeng Z (2010) Labelling algorithms for paired-domination problems in block and interval graphs. J Comb Optim 19:457–470
Chou HH, Ko MT, Ho CW, Chen GH (2008) Node-searching problem on block graphs. Discrete Appl Math 156:55–75
Cockayne EJ (2007) Irredundance, secure domination and maximum degree in trees. Discrete Math 307:12–17
Cockayne EJ, Grobler PJP, Gründlingh WR, Munganga J, van Vuuren JH (2005) Protection of a graph. Util Math 67:19–32
Grobler PJP, Mynhardt CM (2009) Secure domination critical graphs. Discrete Math 309:5820–5827
Haynes TW, Hedetniemi ST, Slater PJ (eds) (1998a) Domination in graphs: advanced topics. Marcel Dekker Inc, New York
Haynes TW, Hedetniemi ST, Slater PJ (1998b) Fundamentals of domination in graphs. Marcel Dekker Inc, New York
Hung RW (2008) Optimal vertex ranking of block graphs. Inf Comput 206:1288–1302
Klostermeyer WF, Mynhardt CM (2008) Secure domination and secure total domination in graphs. Discuss Math Graph Theory 28:267–284
Liu CS, Peng SL, Tang CY (2010) Weak roman domination on block graphs. In: Proceedings of 27th workshop on combinatorial mathematics and computation theory
Merouane HB, Chellali M (2015) On secure domination in graphs. Inf Process Lett 115:786–790
Müller H, Brandstädt A (1987) The NP-completeness of Steiner tree and dominating set for chordal bipartite graphs. Theor Comput Sci 53:257–265
Wang C, Chen L, Lu C (2016) \(k\)-Power domination in block graphs. J Comb Optim 31:865–873
Xu G, Kang L, Shan E, Zhao M (2006) Power domination in block graphs. Theor Comput Sci 359:299–305
Acknowledgements
The authors would like to thank the anonymous referees for their helpful comments leading to improvements in the presentation of the paper.
Author information
Authors and Affiliations
Corresponding author
Additional information
D. Pradhan: Supported in part by DST-SERB Grant under fast track scheme.
Rights and permissions
About this article
Cite this article
Pradhan, D., Jha, A. On computing a minimum secure dominating set in block graphs. J Comb Optim 35, 613–631 (2018). https://doi.org/10.1007/s10878-017-0197-y
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10878-017-0197-y