Abstract
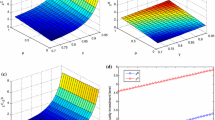
Nowadays, in order to protect information assets, many firms have gradually realized the importance of security investment and information sharing. It is worth pointing out that security breach probability functions play a vital role in firms’ strategic choices. This paper investigates how to determine security investment and information sharing for two firms by employing an alternative well-accepted security breach probability function. In particular, assuming that both firms make their decisions individually, we analyze information sharing, aggregate attack, aggregate defense and the security breach probability at equilibrium. Then we compare these results with those in three (partially) centralized decision cases where a social planner regulates security investment, information sharing or both of them. Between the individual decision case and the partially centralized decision case with the social planner only controlling information sharing, and between the centralized decision case and the other partially centralized decision case, we demonstrate that, although aggregate attack, aggregate defense and the security breach probability remain unchanged, more intervention from the social planner would give rise to higher social welfare. Besides, it turns out that some well-known results of Hausken (Journal of Accounting and Public Policy, 26(6), 639–688, 2007) drastically change in our framework.

Similar content being viewed by others
References
Anderson, R. (2001). Why information security is hard: an economic perspective. Proceedings of the Seventeenth Computer Security Applications Conference, IEEE Computer Society Press, 358–365.
Anderson, R. (2002). Security in open versus closed systems-the dance of Boltzmann, Coase and Moore. Technical report, Cambridge University, England.
Anderson, R., & Moore, T. (2006). The economics of information security. Science, 314, 610–613.
Arora, A., Nandkumar, A., & Telang, R. (2006). Does information security attack frequency increase with vulnerability disclosure?-an empirical analysis. Information Systems Frontiers, 8(5), 350–362.
Bandyopadhyay, T., Jacob, V., & Raghunathan, S. (2010). Information security in networked supply chains: impact of network vulnerability and supply chain integration on incentives to invest. Information Technology and Management, 11(1), 7–23.
Bandyopadhyay, T., Liu, D., Mookerjee, V. S., Wilhite, A. W. (2012). Dynamic competition in IT security: a differential games approach. Information Systems Frontiers, in press, doi:10.1007/s10796-012-9373-x.
Bodin, L. D., Gordon, L. A., & Loeb, M. P. (2005). Evaluating information security investments using the analytic hierarchy process. Communications of the ACM, 48(2), 78–83.
Büyükkarabacak, B., & Valev, N. (2012). Credit information sharing and banking crises: an empirical investigation. Journal of Macroeconomics, 34(3), 788–800.
Campbell, K., Gordon, L. A., Loeb, M. P., & Zhou, L. (2003). The economic cost of publicly announced information security breaches: empirical evidence from the stock market. Journal of Computer Security, 11(3), 431–448.
Cavusoglu, H., & Raghunathan, S. (2004). Configuration of detection software: a comparison of decision and game theory approaches. Decision Analysis, 1(3), 131–148.
Cavusoglu, H., Mishra, B., & Raghunathan, S. (2004). The effect of Internet security breach announcements on market value: capital market reaction for breached firms and Internet security developers. International Journal of Electronic Commerce, 9(1), 69–105.
Cavusoglu, H., Mishra, B., & Raghunathan, S. (2005). The value of intrusion detection systems in information technology security architecture. Information Systems Research, 16(1), 28–46.
Cavusoglu, H., Raghunathan, S., & Yue, W. T. (2008). Decision-theoretic and game-theoretic approaches to IT security investment. Journal of Management Information Systems, 25(2), 281–304.
Cavusoglu, H., Raghunathan, S., & Cavusoglu, H. (2009). Configuration of and interaction between information security technologies: the case of firewalls and intrusion detection systems. Information Systems Research, 20(2), 198–217.
Chai, S., Kim, M., & Rao, H. R. (2011). Firms’ information security investment decisions: stock market evidence of investors’ behavior. Decision Support Systems, 50(4), 651–661.
Clark, D. J., & Riis, C. (1998). Contest success functions: an extension. Economic Theory, 11(1), 201–204.
Cremonini, M., & Nizovtsev, D. (2009). Risks and benefits of signaling information system characteristics to strategic attackers. Journal of Management Information Systems, 26(3), 241–274.
D’Arcy, J., Hovav, A., & Galletta, D. (2009). User awareness of security countermeasures and its impact on information systems misuse: a deterrence approach. Information Systems Research, 20(1), 79–98.
Dutta, A., & Mccrohan, K. (2002). Management’s role in information security in a cyber economy. California Management Review, 45(1), 67–87.
Galbreth, M. R., & Shor, M. (2010). The impact of malicious agents on the enterprise software industry. MIS Quarterly, 34(3), 595–612.
Gal-Or, E., & Ghose, A. (2003). The economic consequences of sharing security information. Proceedings of the Second Workshop on Economics and Information Security, University of Maryland.
Gal-Or, E., & Ghose, A. (2005). The economic incentives for sharing security information. Information Systems Research, 16(2), 186–208.
Gao, X., Zhong, W., & Mei, S. (2012a). On local stability of Cournot models with simultaneous and sequential decisions. Mathematical Social Sciences, 63(3), 207–212.
Gao, X., Zhong, W., Mei, S. (2012b). Stochastic evolutionary game dynamics and their selection mechanisms. Computational Economics, 41(2), 233–247.
Gordon, L. A., & Loeb, M. P. (2002). The economics of information security investment. ACM Transactions on Information and System Security, 5(4), 438–457.
Gordon, L. A., & Loeb, M. P. (2006). Economic aspects of information security: an emerging field of research. Information Systems Frontiers, 8(5), 335–337.
Gordon, L. A., Alumni, E. Y., Loeb, M. P., Lucyshyn, W. (2002). An economics perspective on the sharing of information related to security breaches: Concepts and empirical evidence. Workshop on Economics and Information Security, University of California, Berkeley.
Gordon, L. A., Loeb, M. P., & Lucyshyn, W. (2003a). Sharing information on computer systems security: an economic analysis. Journal of Accounting and Public Policy, 22(6), 461–485.
Gordon, L. A., Loeb, M. P., & Lucyshyn, W. (2003b). Information security expenditures and real options: a wait-and-see approach. Computer Security Journal, 19(2), 1–7.
Hahm, J. H., & Lee, S. (2011). Economic effects of positive credit information sharing: the case of Korea. Applied Economics, 43(30), 4879–4890.
Hamill, J. T., Deckro, R. F., & Kloeber, J. M., Jr. (2005). Evaluating information assurance strategies. Decision Support Systems, 39(3), 463–484.
Hare, F., & Goldstein, J. (2010). The interdependent security problem in the defense industrial base: an agent-based model on a social network. International Journal of Critical Infrastructure Protection, 3(3–4), 128–139.
Hausken, K. (2006a). Income, interdependence, and substitution effects affecting incentives for security investment. Journal of Accounting and Public Policy, 25(6), 629–665.
Hausken, K. (2006b). Returns to information security investment: the effect of alternative information security breach functions on optimal investment and sensitivity to vulnerability. Information Systems Frontiers, 8(5), 338–349.
Hausken, K. (2007). Information sharing among firms and cyber attacks. Journal of Accounting and Public Policy, 26(6), 639–688.
Hausken, K. (2009). Strategic defense and attack of complex networks. International Journal of Performability Engineering, 5(1), 13–30.
Hausken, K. (2012). The economics of terrorism against two targets. Applied Economics Letters, 19(12), 1135–1138.
Heal, G., & Kunreuther, H. (2007). Modeling interdependent risks. Risk Analysis, 27(3), 621–634.
Herath, H., & Harath, T. (2009). Investments in information security: a real options perspective with Bayesian postaudit. Journal of Management Information Systems, 25(3), 337–375.
Huang, D., Qing, H., & Ravi, B. (2008). An economic analysis of the optimal information security investment in the case of a risk-averse firm. International Journal of Production Economics, 114(2), 793–804.
Kallberg, J. G., & Udell, G. F. (2003). The value of private sector business credit information sharing: the US case. Journal of Banking & Finance, 27(3), 449–469.
Kannan, K., & Telang, R. (2005). Market for software vulnerabilities? think again. Management Science, 51(5), 726–740.
Kim, S. H., Wang, Q., & Ulrich, J. B. (2012). A comparative study of cyberattacks. Communications of the ACM, 55(3), 66–73.
Kong, H. K., Kim, T. S., & Kim, J. (2012). An analysis on effects of information security investments: a BSC perspective. Journal of Intelligent Manufacturing, 23(4), 941–953.
Kshetri, N. (2006). The simple economics of cybercrimes. IEEE Security & Privacy, 4(1), 33–39.
Kshetri, N. (2009). Positive externality, increasing returns and the rise in cybercrimes. Communications of the ACM, 52(12), 141–144.
Kunreuther, H., & Heal, G. (2003). Interdependent security. Journal of Risk and Uncertainty, 26(2–3), 231–249.
Lee, M., & Lee, J. (2012). The impact of information security failure on customer behaviors: a study on a large-scale hacking incident on the Internet. Information Systems Frontiers, 14(2), 375–393.
Leeson, P., & Coyne, C. J. (2006). The economics of computer hacking. Journal of Law, Economics and Policy, 1(2), 511–532.
Leininger, W. (1993). More efficient rent-seeking: a Münchhausen solution. Public Choice, 75(1), 43–62.
Liu, D., Ji, Y., & Mookerjee, V. (2011). Knowledge sharing and investment decisions in information security. Decision Support Systems, 52(1), 95–107.
Mookerjee, V., Mookerjee, R., Bensoussan, A., & Yue, W. T. (2011). When hackers talk: managing information security under variable attack rates and knowledge dissemination. Information Systems Research, 22(3), 606–623.
Pardo, T. A., Cresswell, A. M., Thompson, F., & Zhang, J. (2006). Knowledge sharing in cross-boundary information system development in the public sector. Information Technology and Management, 7(4), 293–313.
Png, I. P. L., Wang, C. Y., & Wang, Q. H. (2008). The deterrent and displacement effects of information security enforcement: international evidence. Journal of Management Information Systems, 25(2), 125–144.
Ryan, J. C. H., & Ryan, D. J. (2006). Expected benefits of information security investments. Computers & Security, 25(8), 579–588.
Skaperdas, S. (1996). Contest success functions. Economic Theory, 7(2), 283–290.
Tanaka, H., Matsuura, K., & Sudoh, O. (2005). Vulnerability and information security investment: an empirical analysis of e-local government in Japan. Journal of Accounting and Public Policy, 24(1), 37–59.
Telang, R., & Wattal, S. (2007). An empirical analysis of the impact of software vulnerability announcements on firm stock price. IEEE Transactions on Software Engineering, 33(8), 544–557.
Ulvila, J. W., & Gaffney, J. E. (2004). A decision analysis method for evaluating computer intrusion detection systems. Decision Analysis, 1(1), 35–50.
Wang, J., Chaudhury, A., & Rao, H. R. (2008). A value-at-risk approach to information security investment. Information Systems Research, 19(1), 2008.
Whitman, M. E. (2003). Enemy at the gate: threats to information security. Communications of the ACM, 46(8), 91–95.
Young, R., Zhang, L., & Prybutoka, V. R. (2007). Hacking into the minds of hackers. Information Systems Management, 24(4), 281–287.
Zhang, R. (2011). The role of information sharing in trade credit distribution: evidence from Thailand. Asian-Pacific Economic Literature, 25(1), 133–149.
Zhao, X., Fang, F., & Whinston, A. B. (2008). An economic mechanism for better Internet security. Decision Support Systems, 45(4), 811–821.
Zhuang, J. (2010). Impacts of subsidized security on stability and total social costs of equilibrium solutions in an n-player game with errors. The Engineering Economist, 55(2), 131–149.
Zhuang, J., Bier, V. M., & Gupta, A. (2007). Subsidies in interdependent security with heterogeneous discount rates. The Engineering Economist, 52(1), 1–19.
Acknowledgments
We wish to thank anonymous referees for constructive and informative comments that helped substantially improve the presentation of this manuscript. Financial supports from the National Natural Science Foundation of China (71071033) and the National Pillar Program of China (2012BAH29F01) are gratefully acknowledged.
Author information
Authors and Affiliations
Corresponding author
Appendices
Appendix A. Firms choose security investment and information sharing
The firm’s and the hacker’s expected utilities are respectively
where \( s\left( {{v_1},z_1^a,c_1^a} \right)={v_1}{{\left( {\gamma c_1^a+1} \right)}^{\phi }}{{\left( {\alpha z_1^a+1} \right)}^{{-\beta }}} \), \( s\left( {{v_2},z_2^a,c_2^a} \right)={v_2}{{\left( {\gamma c_2^a+1} \right)}^{\phi }}{{\left( {\alpha z_2^a+1} \right)}^{{-\beta }}} \), c 1 a = c 1 + ρc 2, \( z_1^a={z_1}+\eta {s_2}+\rho \left( {{z_2}+\eta {s_1}} \right) \) and c 2 a = c 2 + ρc 1, \( z_2^a={z_2}+\eta {s_1}+\rho \left( {{z_1}+\eta {s_2}} \right) \).
The first order conditions are given by
Substituting (A1) into (A2) yields
(A3) gives
which, together with (A1), implies
It follows from (A4) and (A5) that
We now validate the second order conditions of the equilibrium. Noting the first order conditions (A1) and (A2), one can easily get at equilibrium
and further
for appropriate interdependence ρ. Therefore, the second order condition for F 1 is satisfied. Analogously, the second order condition for F 2 can be validated.
Noting the first order condition (A4), one can get
and further
for appropriate interdependence ρ. Hence, the second order condition for H is satisfied as well.
Appendix B. The social planner only controls security investment
When only security investment is controlled by the social planner, (A2) and (A3) remain valid. (A1) becomes
which implies
Substituting (B1) into (A2) results in
Combining (B1) with (A4) gives
It follows from (B2) and (B3) that
Now, consider the second order conditions at equilibrium. In a similar way, we can obtain \( {\partial^2}{F_1}/\partial s_1^2 <0\;\mathrm{and}\;{\partial^2}{F_2}/\partial s_2^2<0 \).
Given (B1), it is easy to derive that
and
Analogously, the second order condition for H can be validated.
Appendix C. The social planner just controls information sharing
When only information sharing is controlled by the social planner, (A1) and (A3) remain valid. (A2) becomes
Substituting (A1) into (C1) gives
Aggregate defense and aggregate attack are derived from (A1) and (A3), both of which remain unchanged. Hence, security investment and cyber attacks are given by (A7) and (A8) respectively after substituting s 1 and s 2.
Noting (A1), we have
and
for appropriate interdependence ρ since κ 1 ≥ κ 2 + κ 3. It is obvious that \( {\partial^2}{F_1}/\partial z_1^2<0 \) and \( {\partial^2}{F_2}/\partial z_2^2<0 \). As above, the second order condition for H can be validated in the same way.
Appendix D. The social planner controls both security investment and information sharing
When the social planner controls security investment and information sharing, (B1), (C1) as well as (A4) are valid. Substituting (B1) into (C1) yields
Aggregate defense and aggregate attack in this case are equal to those when the social planner just controlling security investment, which are determined by (B1) and (A4). The security investment and cyber attacks can be obtained similarly, shown in (B4) and (B5) where s 1 and s 2 are replaced. The second order condition for the social planner is satisfied if the following symmetric matrix is negative definite,
where
and other partial derivatives are equal to the preceding after substituting aggregate defense and aggregate attack here. Exchanging the second and the fourth rows and simultaneously exchanging the second and the fourth columns of J(0) yield
where O 2×2 is zero matrix,
and
Obviously, A has two negative eigenvalues. Since
and tr(B) < 0, symmetric matrix B also has two negative eigenvalues. Therefore, all eigenvalues of \( \widehat{J}(0) \) are negative, which implies that J(0) is negative definite since J(0) and \( \widehat{J}(0) \) have the same eigenvalues. By the continuity of J(ρ) with respect to ρ, J(ρ) is negative definite for ρ with a small magnitude (for any non-zero vector X, X T J(0)X > 0 ⇒ X T J(ρ)X > 0 as long as the magnitude of ρ is small). The second order condition for the hacker can be validated similarly.
Rights and permissions
About this article
Cite this article
Gao, X., Zhong, W. & Mei, S. Security investment and information sharing under an alternative security breach probability function. Inf Syst Front 17, 423–438 (2015). https://doi.org/10.1007/s10796-013-9411-3
Published:
Issue Date:
DOI: https://doi.org/10.1007/s10796-013-9411-3